Online Extremist Community Detection
Overview | People | Collaborators | Sponsors | Publications | Tools
Matthew Benigni, Kenneth Joseph, Kathleen M. Carley, 2016, Online Extremist Community Detection: Detecting, Analyzing, and Distrupting Extremist Communities in Social Media, CASOS Summer Institute, Pittsburgh, PA, USA. [pdf]
Benigni, Matthew (2016). Thesis Proposal: Online Extremist Community Detection, Analysis, and Intervention. Carnegie Mellon University, School of Computer Science, Institute for Software Research, June 2016, Doctor of Philosophy, [pdf]
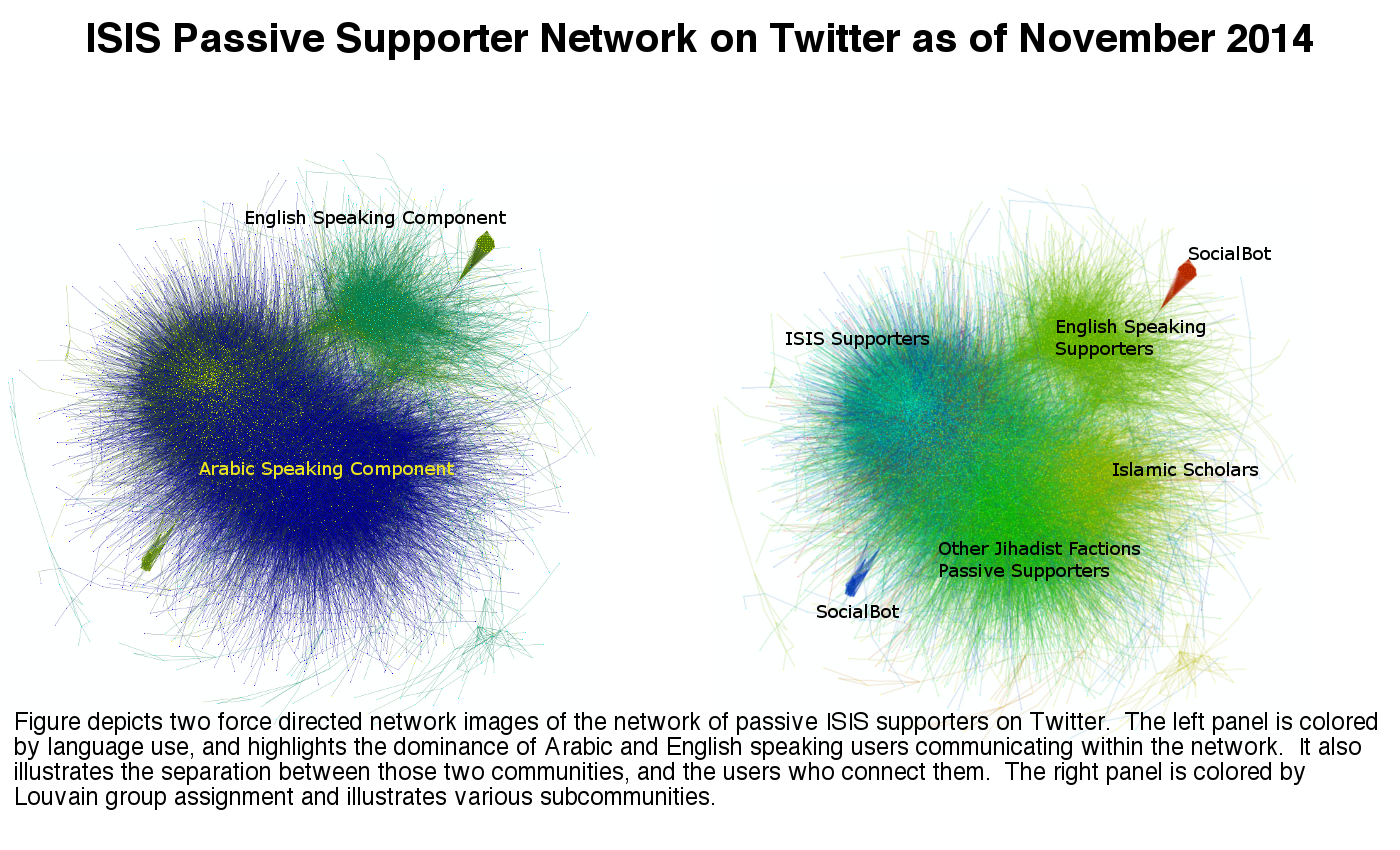
Many covert and terror groups have a strong presence in social media. ISIS, in particular, is well known for its use of social media. The group's ability to proliferate its message using unaffiliated social media users has proven to be an powerful element of their resourcing strategy and is already being immitated by other similar groups like Jabhat al-Nusra. The ability of threat groups to cultivate and utilize large online communities of passive supporters is likely here until we develop effective methods to combat them. Although community detection and covert network detection methods offer methods to identify these groups they often lack the precision required to use them operationally or do not provide the computational scalability to detect these relatively small groups embedded in large social networks. To effectively combat these threat group supporting online communities requires new methodologies to detect them and identify key users and roles.
The ability to use social media and open source public information to identify covert networks and potential recruits could provide critical new capabilities to governments and online social networks. However, detecting this large network from publicly available data is a challenge. In this project we are investigating search techniques utilizing the open source public Twitter under the creative commons license to identify and analyze the ISIS propaganda network.

Figure 1 : Twitter users examined
Standard community detection strategies have difficulty detecting this community of ISIS supporters with adequate precision. We are in the process of developing a web-based interface that will enable the analyst/user to label instances and feed a semi-supervised machine learning algorithm to precisely identify a large proportion of this ISIS supporting network on Twitter. Such an approach and feature set will also facilitate analysis of topical, demographic, and geospatial processes, as well as provide a framework for quantifying network change over time. Our initial results are depicted in Figure 2.
R Source code to this project is available at OSNThreatGroups, as well as a list of de-identified edge lists.